Import Certificates in AD for Smart Card Authentication
As an organization, you may choose to use an internal or external Certificate Authority (CA) for certificate issuance and validation. Active Directory (AD) Certificate Services (CS) will do this by default. If you are not using AD CS, Active Directory must be aware of the CA certificates for certificate issuance and validation (enrollment and authentication). The following instructions will guide administrators on how to configure AD to use the CA certificate chain (root and intermediate).
Publish CA to AD
-
Log on to Domain Controller and copy the two Root CA and SubCA certificates to the desktop.
-
Start a command prompt with Administrator rights.
Publish root CA to Certificate Authorities Container
- Navigate to the following location:
CN=Certificate Authorities,CN=Public Key Services,CN=Services,CN=Configuration,DC=example,DC=local
- Publish the root CA with the
certutilcommand:
certutil -f -dspublish <cert file name> RootCA
Here is an example:
certutil -f -dspublish rootca.cer RootCA
Publish CA Certificates to NTAuthCA Attribute
Publish the certificates for both the root CA and the intermediate CA or sub-CA or Issuing CA into the NTAuthCertificates attribute:
- Navigate to the following location:
CN=Public Key Services,CN=Services,CN=Configuration,DC=example,DC=local
- For each CA (root CA, intermediate CA, sub CA, issuing CA) publish the certificate with the
certutilcommand:
certutil -dspublish -f <cert file name> NTAuthCA
Here is an example:
certutil -dspublish -f rootca.cer NTAuthCA
Publish Intermediate or sub-CA to AIA
Publish the certificates for the intermediate CA or sub-CA or issuing CA into the AIA container:
- Navigate to the following location:
CN=AIA,CN=Public Key Services,CN=Services,CN=Configuration,DC=example,DC=local
- For each intermediate or sub-CA, publish the certificate with the
certutilcommand:
certutil -f -dspublish <cert file name> SubCA
Here is an example:
certutil -f -dspublish subca.cer SubCA
Verify CA Certificates
To verify the CA certificates, you can use either ADSIEDIT or MMC / Enterprise PKI snap-in.
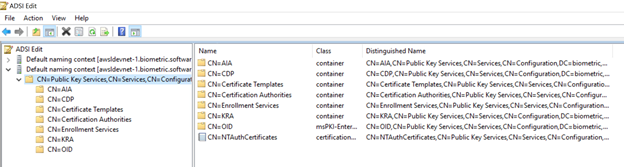
Using ADSIEDIT
-
Start ADSIedit.
-
In Connection Settings, enter a Name and the Path to your domain. Select the Naming Context: Configuration.
-
Browse down to Public Key Services.
-
Look in CN=AIA and verify that only the SubCA certificate is there, not your RootCA.
-
Look in CN=Certificate Authority and verify that only the RootCA certificate is there, not your SubCA.
-
Look in CN=NTAuthCertificates and verify that your CA certificates are there.
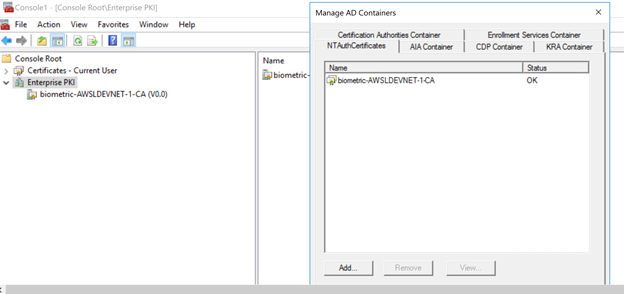
Using MMC / Enterprise PKI Snap-in
-
Start the Microsoft Management Console (MMC).
-
Load the snap-in Enterprise PKI.
-
Right-click on the snap-in and select Manage AD Containers.
-
Click on each container and verify that your certificates are there.
Remove CA Certificates from the Desktop
When the CA certificates are published, remove the CA certificates from the desktop.