Configuring Outcome: Entra ID Temporary Access Pass (TAP)
Some functionality is limited. This article is subject to change as the feature develops and we make improvements.
At least one Entra ID integration must be enabled via HYPR. See Integrations for instructions on how to accomplish this step.
If you do not have a qualifying Entra ID integration, HYPR Affirm will display this message when you try to do anything:
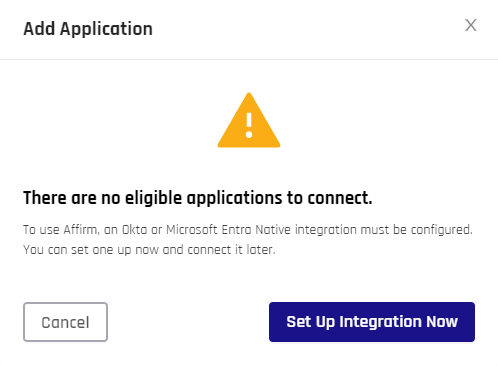
Click Set Up Integration Now to open the Control Center Standard: Integrations options.
Click Cancel to return to HYPR Affirm.
For HYPR Affirm to work with the integration fully, the IdP must include the following attributes for all target users:
- Username (UPN field for Entra ID)
- Email Address
Depending on the specific verification flow configuration, HYPR Affirm requires the following additional attributes:
- Mobile Phone Number (Phone Number Verification step)
- First and Last Name (Identity Verification step)
- Manager Information (required if Approver type of Manager is set)
- Street Address, City, State, Postal Code, and Country Code (Location step)
Identity Verification (IdV) flow configuration where Microsoft Entra ID Temporary Access Pass is used as a requester outcome is located in Administering HYPR Affirm.
This guide explains how to configure Microsoft Entra ID so HYPR Affirm can issue a Temporary Access Pass (TAP) after a requester successfully completes a verification flow.
The primary setup flow for this article is based on the internal HYPR Affirm-only Entra integration guide and uses Microsoft's TAP documentation as supplemental background for tenant-side TAP policy behavior.
The assumption is that you want HYPR Affirm to issue a Microsoft Entra Temporary Access Pass as the outcome of a successful verification flow, especially when you do not already have a Microsoft Entra integration in HYPR that is being used by another login experience.
What You'll Need
Make sure you have the following available:
- A Microsoft Entra tenant
- An administrator account in the
*.onmicrosoft.comdomain with Global Admin access - A HYPR tenant with HYPR Affirm enabled
- A decision on whether this Entra integration will be used only for Affirm or shared with other HYPR use cases
Setting Up the Entra ID Tenant
Enable the Temporary Access Pass Policy
Before HYPR can issue a TAP, the Entra tenant must allow TAP for the users or groups that will go through the Affirm workflow.
- Sign in to the Microsoft Entra admin center as an administrator with permission to manage Authentication methods policies.
- Browse to Entra ID > Authentication methods > Policies.
- Select Temporary Access Pass.
- Enable the policy and include the users or groups that should be allowed to sign in with TAP.
- If necessary, select Configure and adjust the policy defaults, such as minimum lifetime, maximum lifetime, default lifetime, passcode length, and whether TAP is one-time use.
- Click Save.
HYPR can create and return a TAP only if the target user is in scope for the Entra TAP policy.
If your requesters will use TAP to enroll a device or complete passwordless registration after the verification flow, review the lifetime and one-time-use settings carefully. Microsoft's guidance notes that one-time TAPs can require tighter timing during passwordless registration, while multi-use TAPs can simplify longer onboarding flows.
HYPR can issue a TAP only for users who are allowed to use TAP in the Entra tenant. For additional details on TAP policy options, onboarding, and lifecycle considerations, review Microsoft's guidance in Configure Temporary Access Pass to register passwordless authentication methods.
Register Application
Register an Entra application that HYPR will use to call Microsoft Graph on behalf of the integration.
- In the Microsoft Entra admin center, go to Entra ID > App registrations.
- Click New registration.
- Enter an application name such as
HYPRAuthApp. - Select Accounts in this organizational directory only.
- Complete the registration.
- On the application Overview page, make a note of the following values:
- Application (client) ID
- Directory (tenant) ID
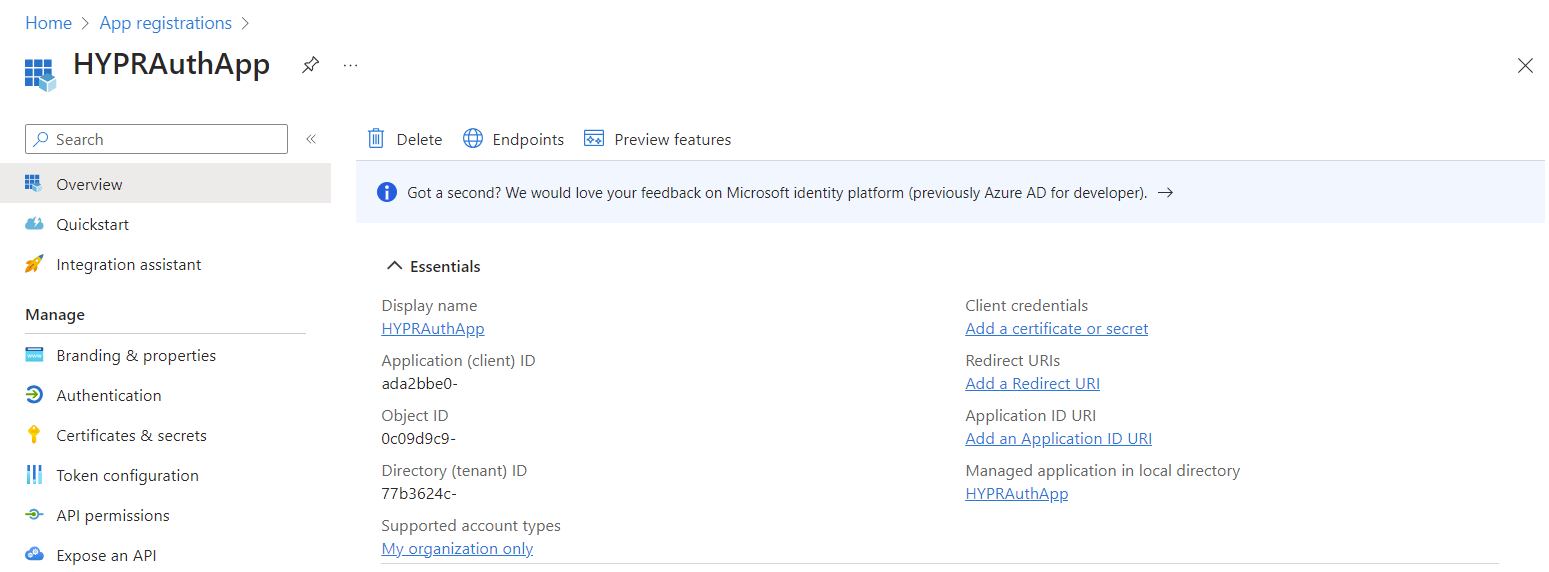
You will use these values later when you add the Entra integration in HYPR Control Center.
Grant Required API Permissions
The Entra application used for this outcome must be able to read directory information and create Temporary Access Pass methods.
- Open the application you just registered.
- Go to API permissions.
- If the default
User.Readpermission is present and you do not need it for this integration, remove it. - Click + Add a permission.
- Select Microsoft Graph.
- Select Delegated permissions.
- Add the following permissions:
Directory.Read.AllUserAuthenticationMethod.ReadWrite.All
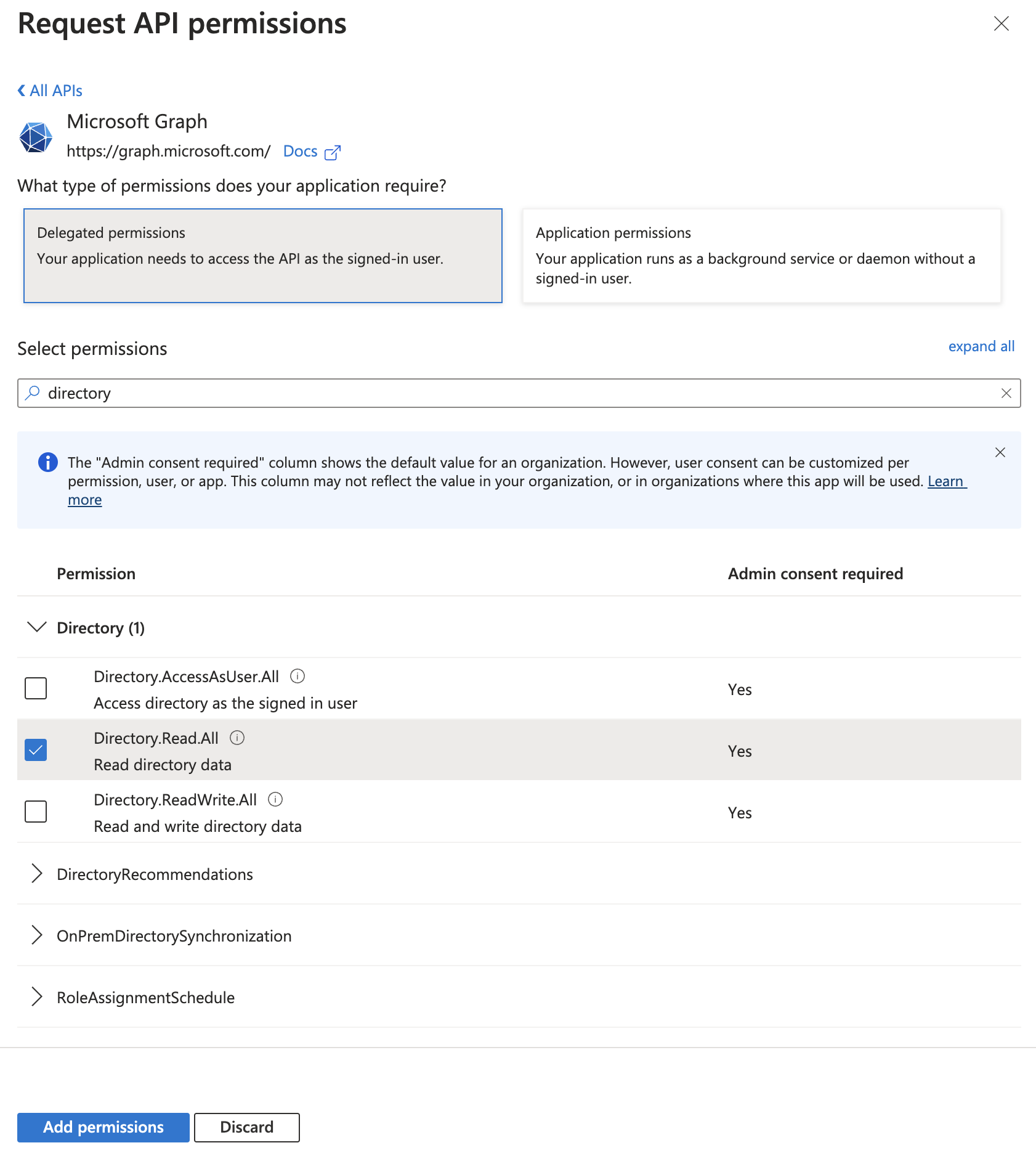
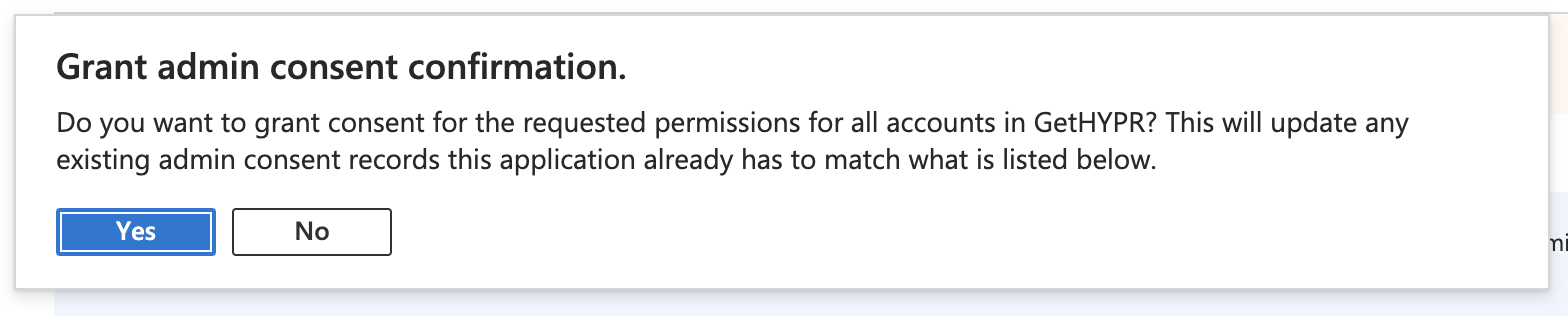
- Back on the API permissions page, click Grant admin consent and confirm the prompt.
Sometimes Entra ID will immediately assume Delegated permissions and skip the permission-type selection screen. That is acceptable for this workflow; you can confirm the permission type after admin consent is granted.
These permission requirements and the overall setup sequence are based on the HYPR Affirm-only Entra integration flow. The Microsoft documentation linked earlier is useful for understanding TAP policy behavior, but the HYPR-specific application and Control Center steps are driven by the HYPR integration flow described here.
Create a Client Secret
HYPR Control Center can use either a client secret or a client certificate to authenticate to Microsoft Graph, depending on which authentication method you select in the Entra integration form.
- Open the Entra application.
- Select Certificates & secrets.
- Click New client secret.
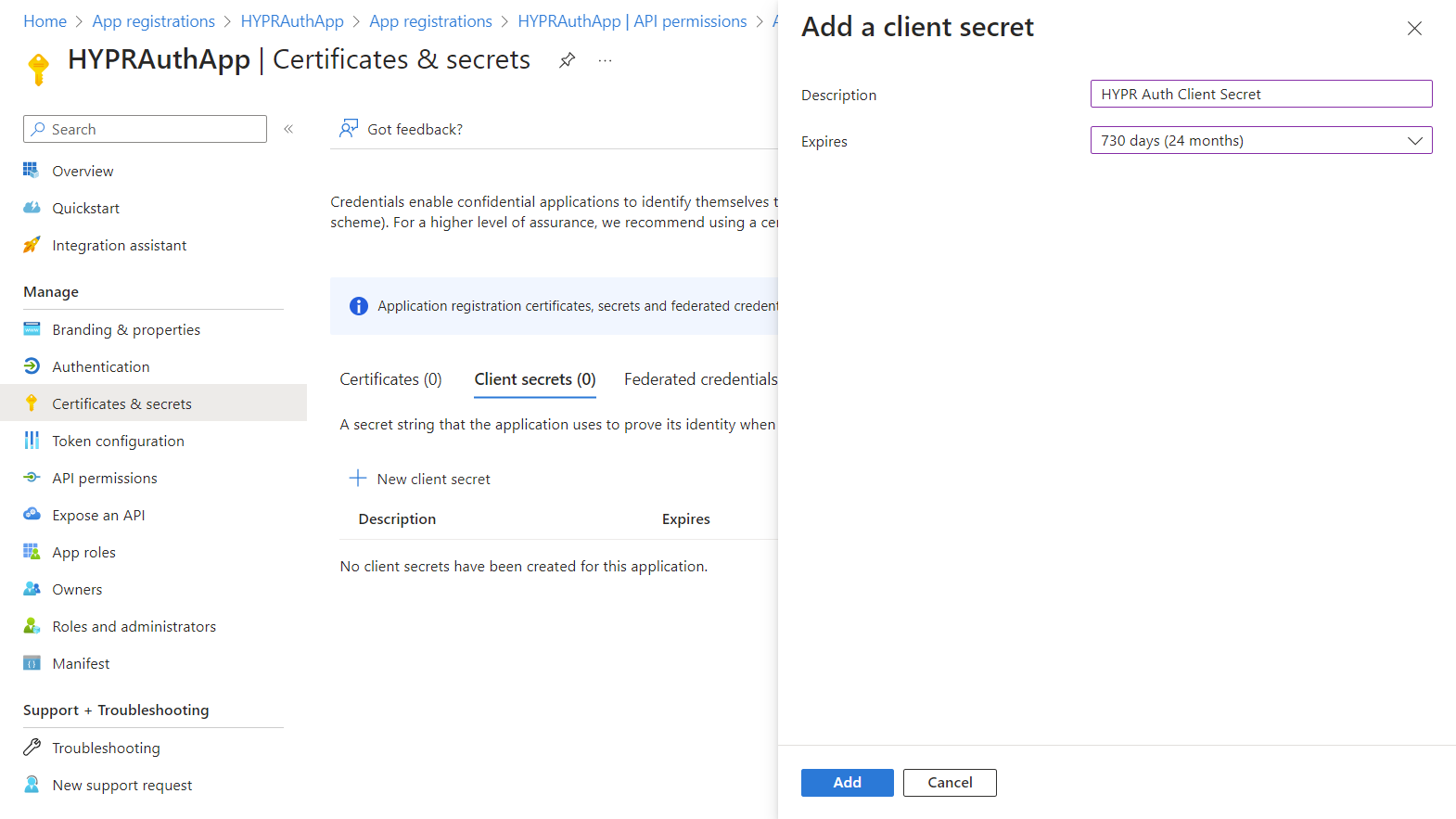
- Enter a Description and choose an expiration period.
- Click Add.
- Copy and save the client secret value immediately.
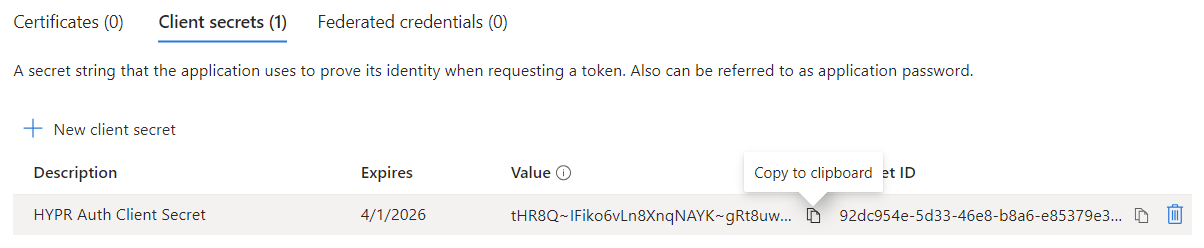
If you return to this screen later, Entra ID masks the client secret value and you will need to create a new one.
Setting Up the HYPR Tenant
Install the Integration
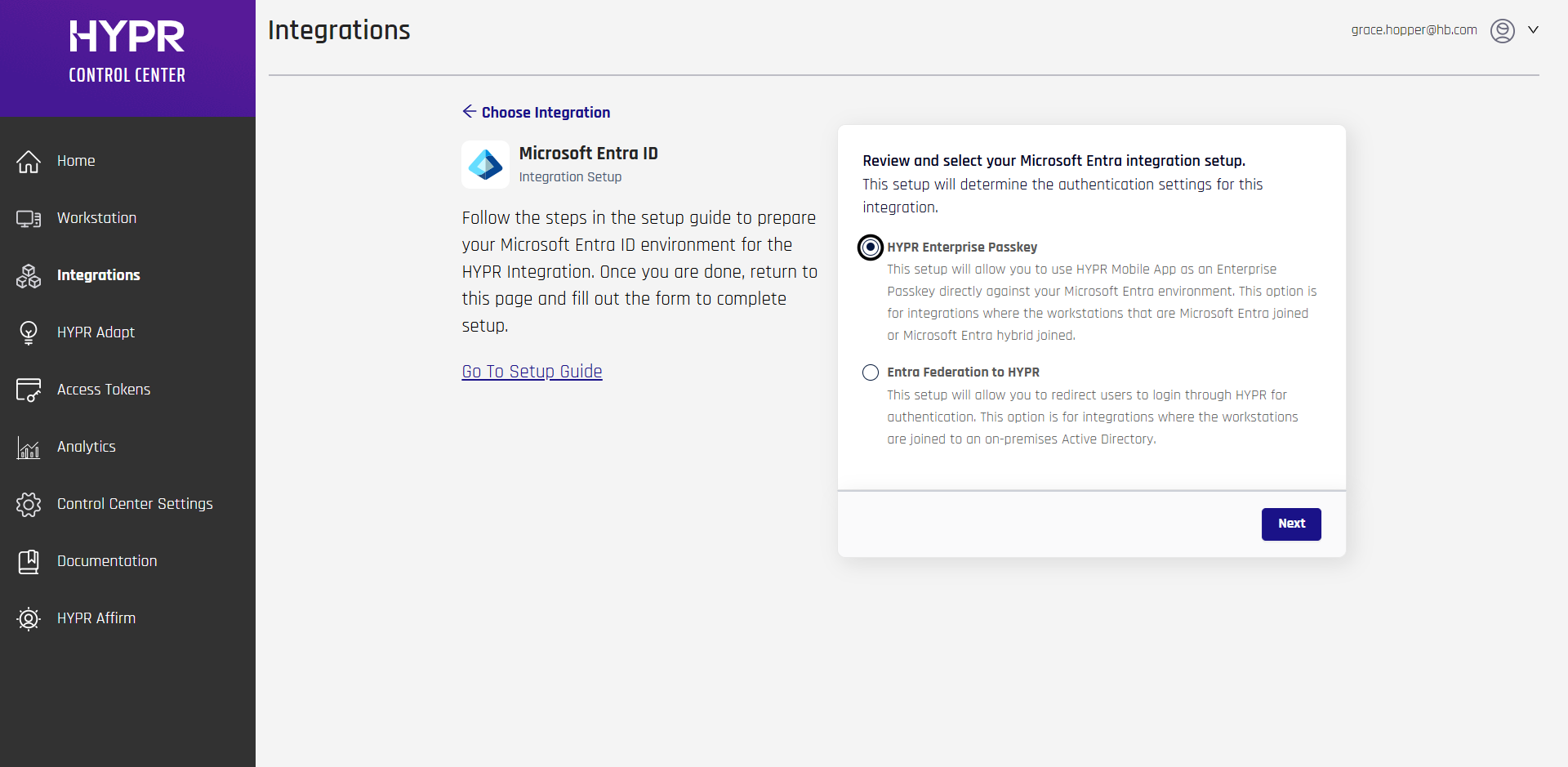
Once Entra ID is ready, add the corresponding Entra integration in HYPR Control Center.
-
In HYPR Control Center, go to Integrations > Add New Integrations > Microsoft Entra ID.
-
After selecting the Entra integration, HYPR displays a setup-choice dialog titled Review and select your Microsoft Entra integration setup.
For this TAP outcome configuration, select HYPR Enterprise Passkey.
- Complete the setup form using the values collected earlier:
- Application Name
- Directory (tenant) ID
- Application (client) ID
- Authentication Method: Certificate or Client Secret
- Client Secret if Client Secret authentication is selected
- Client Certificate and Client Private Key if Certificate authentication is selected
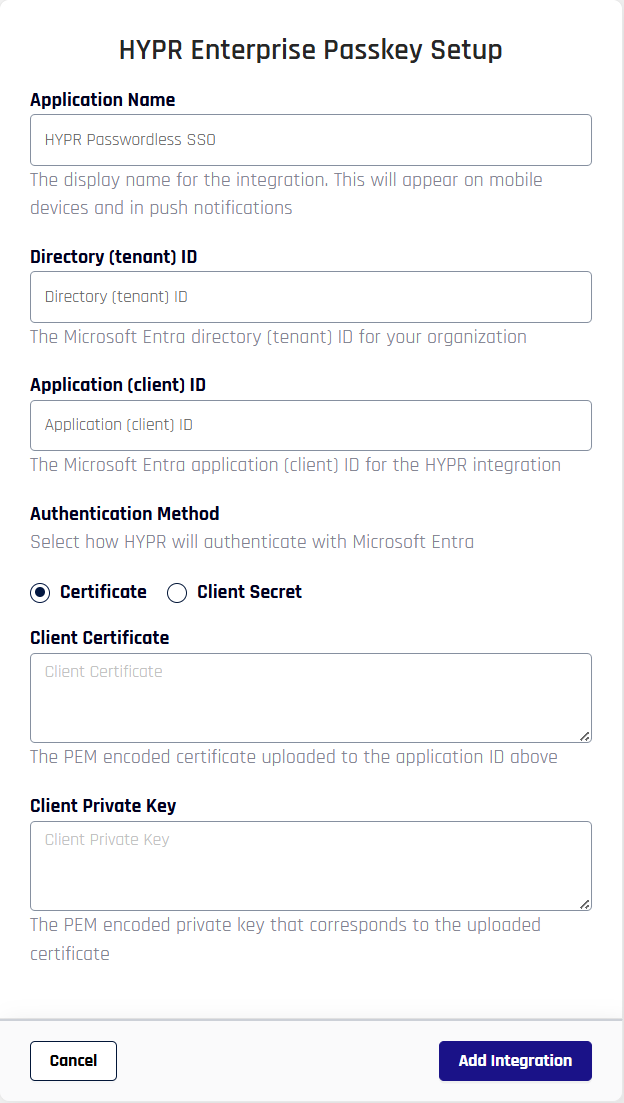
- Click Add Integration.
- If setup succeeds, HYPR confirms that the provided values are valid and that it can connect to Entra ID.
- When HYPR displays the post-setup confirmation dialog, click Maybe Later unless you specifically want to continue with self-enrollment.
If you select HYPR Enterprise Passkey, HYPR also creates Entra groups used by that integration. If you are creating the integration only to support HYPR Affirm TAP outcomes, you do not need to manage those groups directly.
Configure Affirm to Use the Integration
After the Entra integration exists, assign it to the HYPR Affirm workflow that should issue TAPs.
- Open HYPR Affirm in Control Center.
- Open the target verification flow.
- In the Applications section, add the Entra application associated with the integration you created.
- In the workflow Outcome section, select Issue a Microsoft Entra ID Temporary Access Pass (TAP).
- Save the workflow.
For more information about the overall workflow configuration, see Administering HYPR Affirm.
Validate the Configuration
After the workflow is configured, run a test verification against a user who is in scope for the Entra TAP policy.
Successful validation should confirm the following:
- The verification flow completes successfully
- The configured workflow returns the TAP outcome
- The requester receives the Temporary Access Pass result
- The TAP can be used in accordance with your Entra tenant's TAP policy
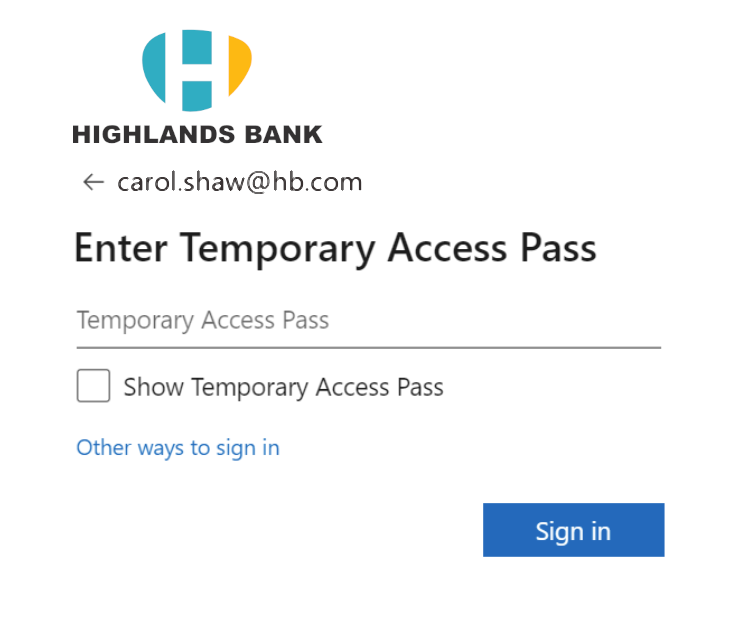
The requester experience will look similar to this when the TAP outcome is returned:
If you need guidance on how users can use the issued TAP after the Affirm workflow completes, see Microsoft's public TAP documentation: Configure Temporary Access Pass to register passwordless authentication methods.
Related Documentation
- For general HYPR Affirm workflow configuration, see Administering HYPR Affirm
- For another Entra-based outcome example, see Configuring Outcome: Entra ID Verified ID
- For requester-side experience, see HYPR Affirm Requester Experience