Access Tokens
HYPR Control Center Advanced: Advanced Config Menu
The HYPR Control Center exposes an extensive set of APIs which use access tokens as an authentication and authorization mechanism.
API access tokens can be created and revoked by Control Center admin users as described below. Tokens have an expiration period (TTL) of 30 days. The expiration date is reset to the current date+TTL each time you use the token, so if you don't use the token for more than 30 days it will expire and you'll need to generate a new one.
Token Scope
Every token is bound to a specific RP Application. Any operation within the RP Application is allowed in the presence of a valid token.
API Tokens
The Control Center exposes a set of APIs you can use to perform user management tasks programmatically rather than through the UI. For example, you could create a script that deletes workstation users through an API request rather than through the Control Center. Please see the API documentation for more information.
The APIs use access tokens as an authorization mechanism for your API requests. As an administrator, you’ll need to create an access token through the Control Center then include the token in every API request you submit.
API access tokens can be used in the following cases:
- API requests for the Workstation user APIs, which require a token of type
access-tokenDefaultApp. To create this type of access token, select HYPR Default Workstation Application (HYPRDefaultWorkstationApplication) as the Application during token creation. - API requests for the Control Center Admin APIs , which require a token of type
CCAdminAccessToken. To create this type of access token, select Control Center Admin (controlCenterAdmin) as the Application during token creation. - API requests for Integrations you’ve created through the Integrations section in the Control Center, for example an Okta integration. For this type of access token, the Application you select during token creation is the name you gave the integration when you created it.
Workstation Installation Tokens
These tokens are used during the installation process for the HYPR Passwordless client. Whenever you install the HYPR Passwordless client, either for yourself or for other users, you must provide a Workstation Installation token (also called an endpoint security token). See the HYPR Passwordless client Installation instructions for more information. However, this token is given to you by HYPR after you sign up for the service and should not be changed. You use the same token for all installs. Typically you don’t need to create a token manually for this purpose. However, HYPR Support may occasionally ask you to create one.
Create Access Token
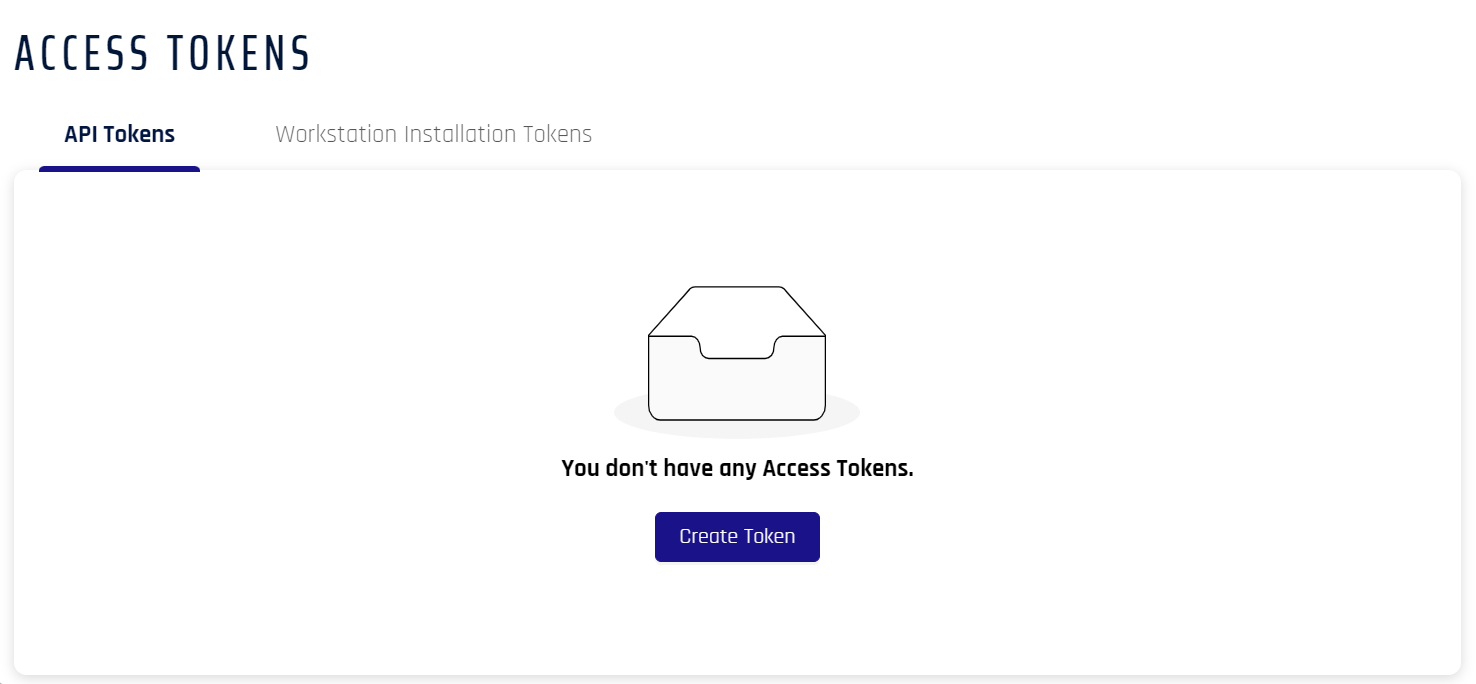
- In the selected RP Application left menu, open Access Tokens
- Click Create Token.
-
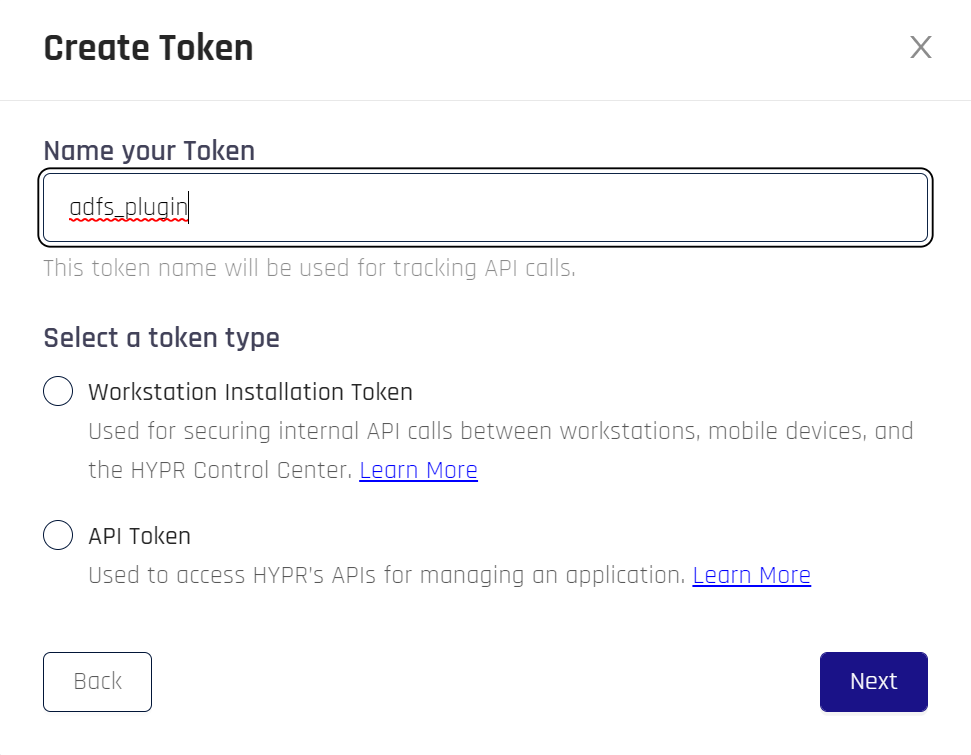
The Create Token dialog opens. Name the token, then Select a token type:
- Workstation Installation Token
- API Token
When finished, click Next.
- If you made a Workstation Token, skip this step. For API Tokens, you must assign Permission Types to the token. This will limit the functions that may be performed using the token. Once you have assigned Permission Types, click Next.
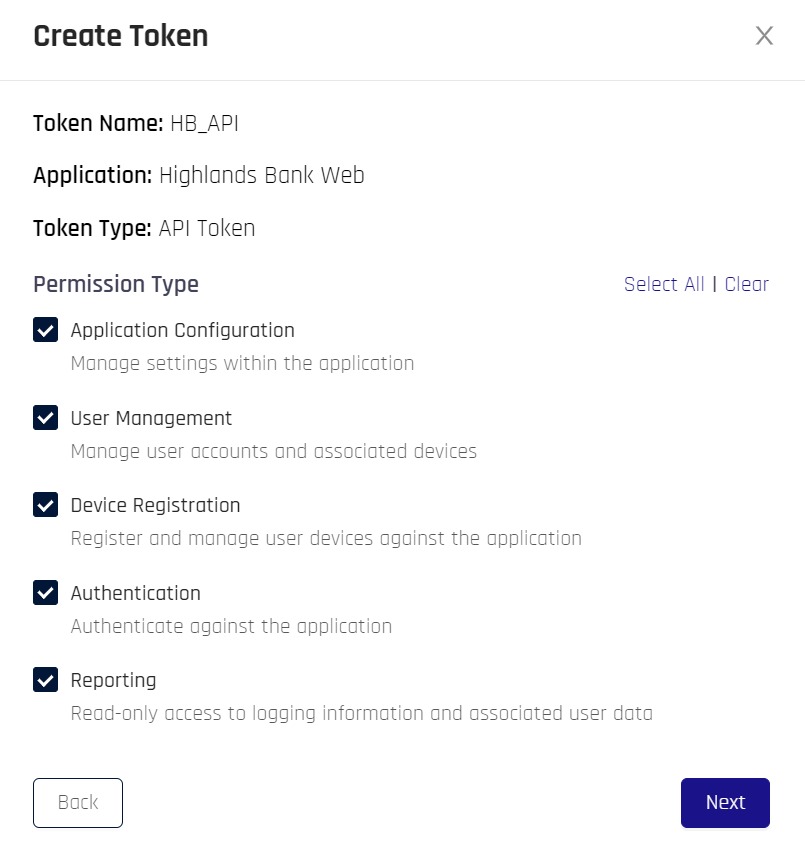
-
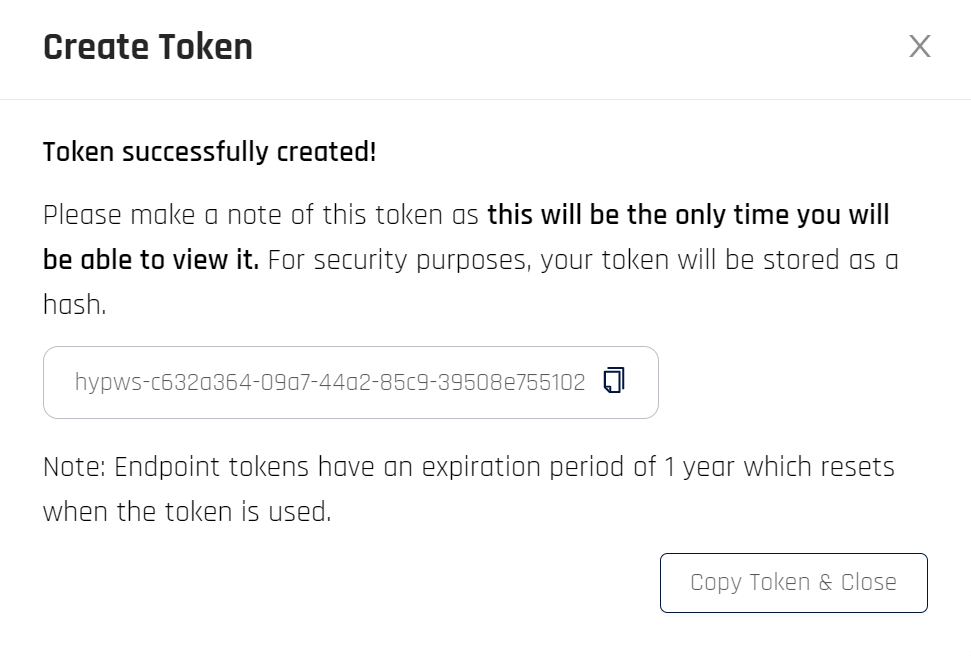
This step provides the option to copy the generated access token. This is a one-time action; the token is never displayed again beyond this dialog.
Click Copy Token & Close when finished.
- The following table displays. Click the appropriate tab to see information for each types of token.
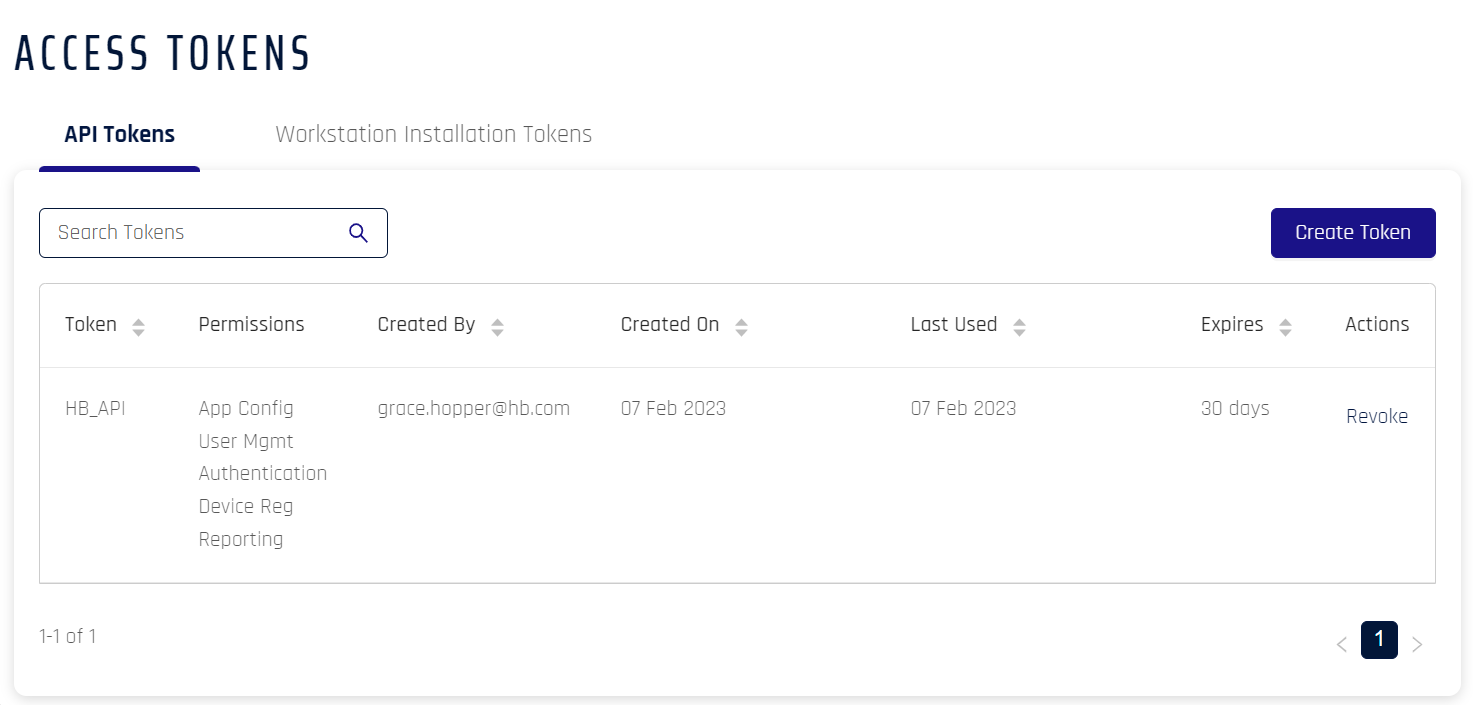
| Field Name | Description |
|---|---|
| Token | Name of the token |
| Permissions | Access to functions within Control Center. Possible Values: App Config | User Mgmt | Authentication | Device Reg | Reporting |
| Created By | Creator of the token |
| Created On | Date of creation |
| Last Used | Last used by the clients for registration/authentication and de-registration |
| Expires | Time left before the token expires. This value resets to 30 days after each use; if not used within 30 days of the last use, it will expire and a new token will need to be issued |
| Actions | The only available action as of this version is to Revoke the token |
Double Vision
These tokens can also be managed from the Control Center Standard Mode Access Tokens list.
Use the Access Token
An access token is provided on every request to the HYPR API HTTP endpoint. The request will fail if the token is missing or does not have permissions for the requested operation. The request will also fail if the token has expired, been revoked, or is invalid.
The access token must be sent in the Authorization header using the Bearer schema.
Here is an example of how to pass an access token using the cURL command. In the following example, the access token is 7c839b65-9d28-4037-afc6-993fc5595cbf.
curl https://staging1.gethypr.com/cc/api/stats/authenticator/logins \
-H 'Authorization: Bearer 7c839b65-9d28-4037-afc6-993fc5595cbf'
Revoking an Access Token
When you revoke an API access token, you’ll no longer be able to submit API calls for the entity to which the token applies (for example, an integration). In most cases, you won’t need to revoke access tokens. In some cases, HYPR Support may ask you to perform this task.
Risky Revocation
Avoid revoking a Workstation Installation token unless HYPR Support recommends it. This token is used during the installation process for the HYPR Passwordless client. Although installations you’ve performed already won’t be affected if you revoke the token (the HYPR Passwordless client will run as usual for everybody), you won’t be able to install the HYPR Passwordless client for any new users. See the HYPR Passwordless Installation instructions for details.
To revoke an access token, complete these steps:
- Click Access Tokens in the Control Center left navigation pane.
- Locate the access token you want to revoke.
- Click Revoke in the Actions column of that token.
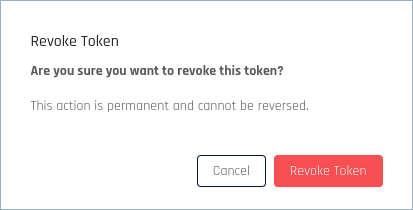
- In the confirmation dialog, click Revoke Access Token.
Related Articles
Updated about 1 month ago
